About Us
Access Network Solutions was founded in 1996 by Robert Faulhaber to provide Information Technology solutions to businesses and corporations helping them manage the ever-changing technology landscape in today’s business environment.
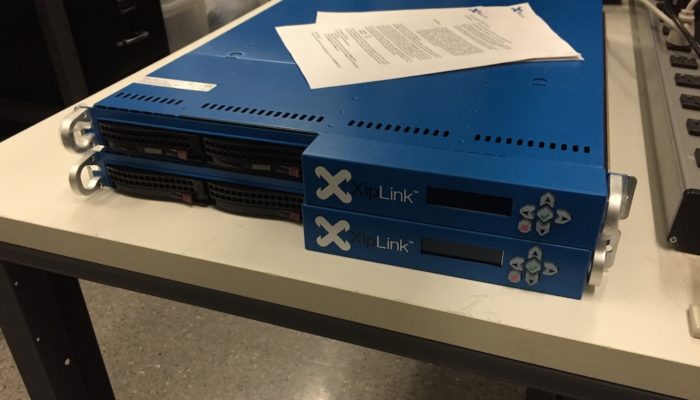
Having designed, deployed and worked on communications systems and networks for organizations such as ITT and Antarctic Support Associates in far-flung locations such as Saudi Arabia and Antarctica, Access Network Solutions was formed using that knowledge and experience to provide clients with the ability to use technology to advance and grow their businesses.
Our staff has extensive experience in network infrastructure design, engineering and implementation, and the ability to provide technical solutions for your current business needs and helping you plan not only for your needs today but also for tomorrow.